Real Time Intruion Alert & Active Response System Using Wazuh Integrated with Telegram Bot Chat
→ View detailed version on GitHub
I built this as a final project for my CyberAnalyst class at CCIT-FTUI. The premise was simple: what if a security analyst could get notified of an attack and respond to it all from their phone, without touching the server? That’s exactly what this does.
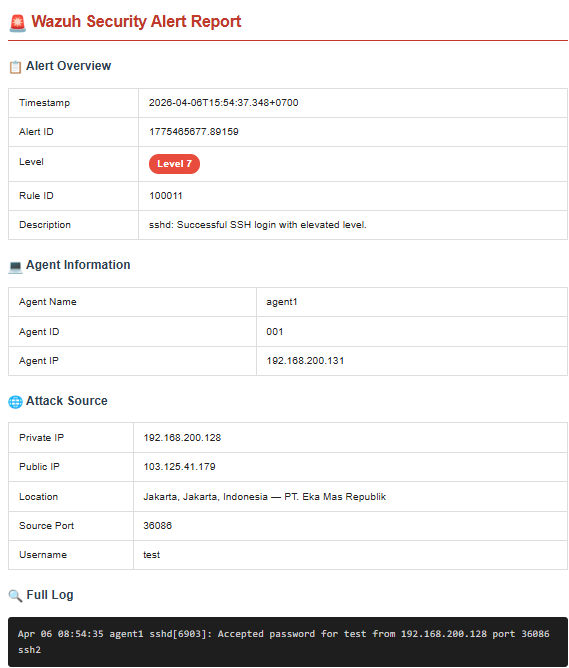
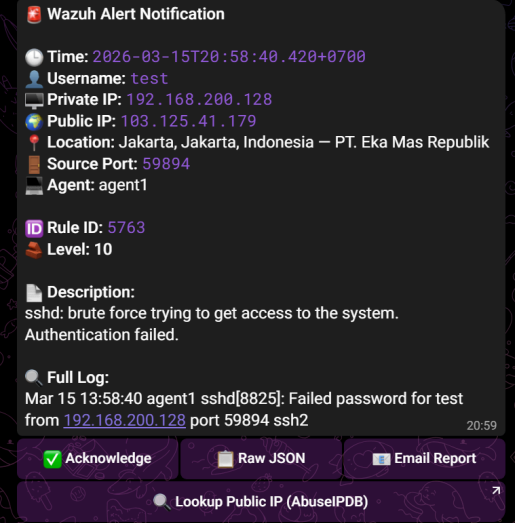
A Wazuh SIEM instance monitored by a custom Telegram bot. When Wazuh detects something suspicious — SSH brute force, privilege escalation, suspicious commands — it fires an alert straight to Telegram with full context: source IP, geolocation, rule ID, MITRE ATT&CK mapping, and the raw syslog entry.
From that same Telegram message, you can:
- Acknowledge the alert
- View the raw JSON directly in chat (or as a file if it’s too large)
- Send an HTML email report to a recipient of your choice
- Lookup the public IP on AbuseIPDB with one tap
And via slash commands:
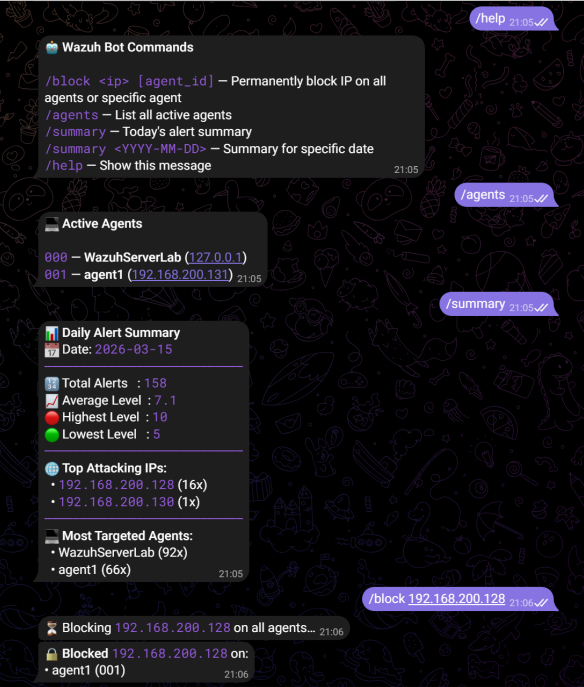
/block 192.168.200.128 # permanent iptables drop via active response
/agents # list all active Wazuh agents
/summary # today's alert digest
/summary 2026-03-15 # historical summary by dateHTML email report